8 essential WordPress security secrets
Prevent, deter and recover from attacks on your WordPress site with these must-know tips.
Over the past 15 years WordPress has become the world's most popular content management system. Easy to get started with and extremely versatile, it's one of the best blogging platforms around – the ideal home for your design portfolio, or something more ambitious.
There's a huge assortment of WordPress themes to choose from, while if you're unafraid of a bit of code you'll find loads of WordPress tutorials that'll help you get to grips with its more complex features. For other options, try our guides to the best website builder and web hosting service.
A big drawback of WordPress's popularity, however, is that it's a prime target for hackers. If you want to avoid losing control of your shiny new site, follow these tips for keeping it secure.
01. Add extra security to user accounts

A great deal of vulnerability comes from the user accounts that intentionally give access to your site, particularly administrator and editor roles. If a hacker gains access to one of these accounts, of any user on the site not just the main admin's one, then they can make changes at will on the website.
Always make sure accounts only have the access they need. For example, if a user is only going to be writing articles, consider giving them only contributor or editor access, never administration. Keep in mind the level of ability of your users, ensuring that anyone with admin or editor access is fully trained to use all the account's features to avoid accidents.
You can add features to allow temporary access to a certain role level, i.e. if you have a contractor working on the site and they need temporary admin access, you could give it to them with a set time to expire so that you don't need to remember to revoke their access later down the line.
If a certain role level does not need all of the default permissions, you can install a roles and permissions plugin to turn off certain permissions that will never be used. You can also create other roles with only specific access. Restrict users to only the permissions they need to avoid accidental or intentional misuse of a feature.
Sign up to Creative Bloq's daily newsletter, which brings you the latest news and inspiration from the worlds of art, design and technology.
To help prevent attacks coming from user logins, put a limit on the number of times an account can make a failed login attempt before that username is locked out for a period of time. This mostly catches out bots who are guessing passwords, but remember to warn your users that they should not attempt to log in more than the number of times you set in a row. If they can't remember their password, and if they forget their password, they should reset it instead of trying to guess!
It's also good practice to remind users to use secure passwords (over eight digits, with upper, lowercase, numbers etc), and to change them every so often. Remind them never to write their passwords down, and log out when they are finished with their session to avoid unauthorised access to their accounts.
Two-factor authentication is an extra level of security that can be added to logins. They require users to use their authenticators when logging in to increase the number of credentials needed from just the standard. Users will need an extra code or pin to log in, usually randomly generated by an app or sent to a phone by text. It can feel like an extra barrier to login for users, but it's also an extra barrier for hackers.
02. Change old defaults
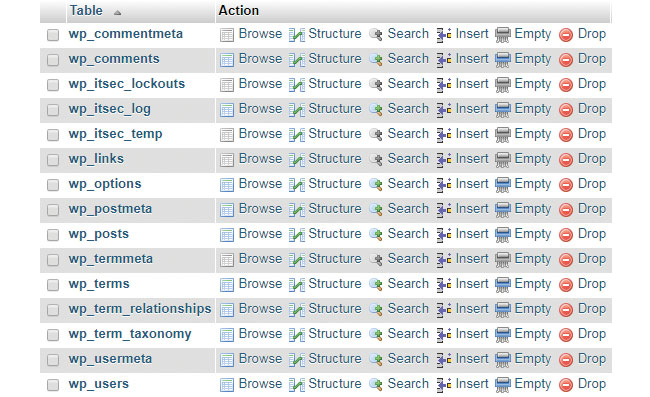
New WordPress installs make you choose a custom username for your admin account, but if you installed your site a while ago, your admin account may have the default name of 'admin' – this makes it easier for hackers to guess your login credentials as half the work is already done for them. Change the default admin username to something else to improve security. You can do this manually via the database in the wp_users table, or you can create a new admin profile and delete the old one via the Admin panel (be sure to attribute all the old account posts to the new one).
You can also change the default database prefix to something other than wp_ to add a further layer of obscurity to your default setups. The easiest way to do this on an existing install is via a plugin, but backup your databases first.
03. Keep WordPress updated

WordPress is always updating and improving its built-in security, so make sure that your version is the most up to date to stay ahead of old vulnerabilities and exploits. Most WordPress installations update automatically, but if yours doesn't, keep an eye on your Admin panel or Inbox to be notified of when new updates are ready to install. Hackers are on the lookout for sites that haven't been updated, and only 22% of WordPress sites are running the latest version. Since WordPress runs almost 30% of all websites on the web, that's a lot of outdated websites!
If you're running a staging site, you can test all updates for compatibility with your current theme and plugins before pushing live. This is good practice to avoid any automatic updates accidentally conflicting with existing installations. It gives you a chance to catch any problems before going into production. Don't forget to update your Plugins and Themes too. It's not just old core WordPress vulnerabilities that can give hackers a way in; anything you install on your WordPress website needs to be secure as well. The next tip will tell you more on choosing trustworthy plugins.
04. Install trusted plugins and house clean regularly
There's a temptation to install as many plugins as you have problems to solve, but too many plugins can cause bloat and one unreliable plugin can cause a security risk. Always check that plugins are trustworthy before installing. Download through the official WordPress interface or website, and always check the star rating and reviews for negative feedback that may indicate a security flaw.
Plugins are created by developers with all different levels of ability. Even though plugins are vetted before being added to the WordPress site, you should always do your own research to make sure the code you are installing is solid.
The WordPress website will tell you how old a plugin is, when it was last updated, and most importantly, if it's compatible with your version of WordPress. A plugin that has not been updated in a while is not necessarily a bad one, it may just mean it hasn't needed an updated in that time. Check for recent reviews to confirm the plugin is still viable, and that it's still compatible with your version. An old plugin with recent low star reviews and an unknown compatibility is worth avoiding.
Regularly delete unused themes and plugins, as even a deactivated plugin can be a security risk if a vulnerability is found and exploited. Keep your plugin directory clean. You should only have plugins installed that you are currently using. Check older plugins when you update to see if they're still compatible.
Review your plugins periodically to make sure you still have the best one for the job. There could be a new plugin that combines the features of a few that you already have and might be better supported, more secure and easier to maintain.
05. Consider managed hosting

It's not just the security of your own site you need to think about. If you host your sites on shared servers, you run the risk of cross-server contamination, where hackers gain access through a different site and are able to damage other sites sharing the same space. Consider managed hosting or Virtual Private Server (VPS) hosting to eliminate this threat, where your site is hosted separately.
Cost is an obvious implication, but for sites with high loads and traffic, dedicated servers can improve performance as well as security. Different hosts have different solutions; compare a few to assess which best suits your needs.
06. Mask, lock and hide
Hackers have less leverage if they don't know where to start. Hide your WordPress version number from your code so only admins know which version of WordPress you're running. That way, hackers don't know which vulnerabilities are present to exploit.
Move your login page from /wp-login to something that's not default. This makes a huge stumbling block for DOS and brute force attack bots that trawl sites looking for login forms to target. It also adds a more aesthetic value, in that you can change the URL to something more memorable for your users.
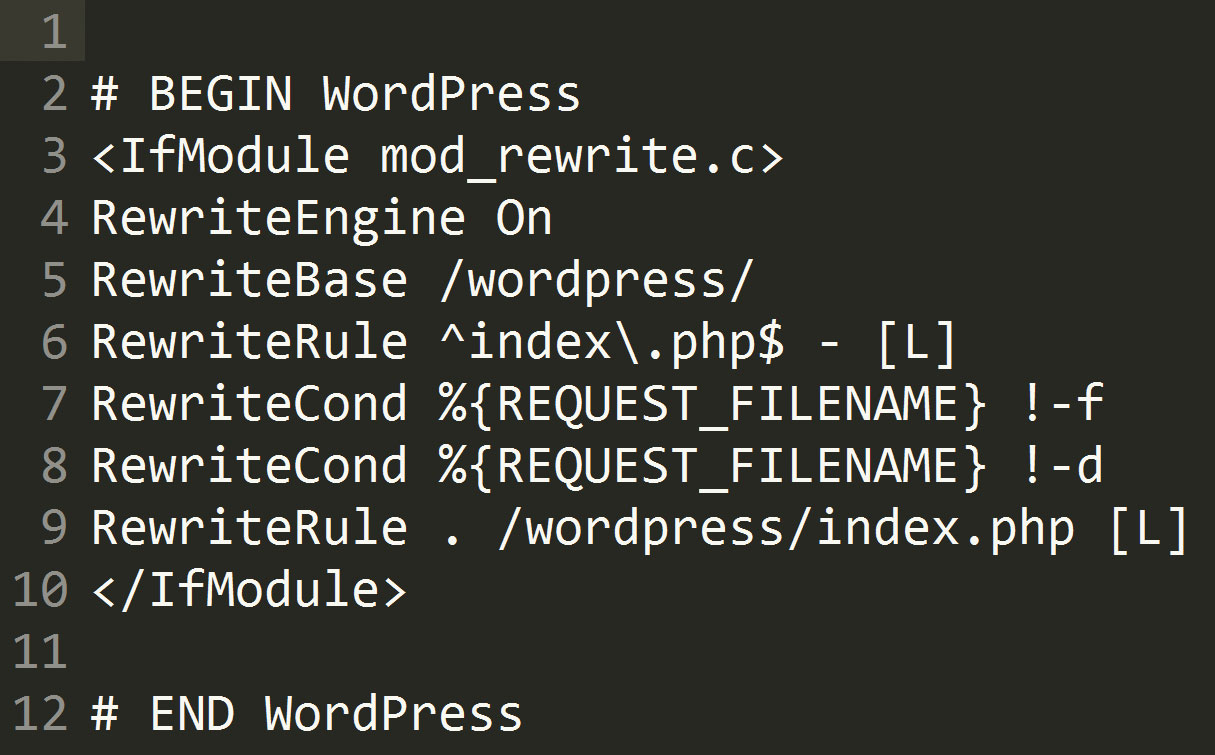
Deny external access to wp-config.php and .htaccess using the following code in your .htaccess file:
<Files wp-config.php>
order allow,deny
deny from all
</Files>
<Files .htaccess>
order allow,deny
deny from all
</Files>You can also disable file editing from the Admin panel if you know that your themes are only going to be edited via file uploads on an FTP. This prevents anyone with access to the Admin panel from directly editing files accidently or as a hacker with malicious intent. Insert the following into your wp-config.php file:
define('DISALLOW_FILE_EDIT', true);07. Run backups frequently
Make sure that your site is backed up in the event that your site is hacked and you need to roll back to an earlier clean version. How often you should run backups depends on how often your site is updated.
It's integral to back up in a place where your site isn't hosted to avoid any malicious activity on your WordPress hosting from infecting your backups too. Backups can be stored on your own computer or a cloud-based service like Google Drive, Dropbox or Amazon S3 (check out other cloud storage options here).
Backing up in a location that is not your current server also helps if you have an unresolvable plugin or theme conflict and can't access your site, or if there's a catastrophic server malfunction and you lose all your work.
Dedicated backup plugins exist to help you keep on track, most with options for scheduled or manual backups. Free and premium versions give you various options, BackupBuddy being the most popular paid service as they have their own third-party storage for your files, plus the ability to restore from a backup directly. Compare other plugins like UpdraftPlus and BackWPup for their free and premium versions to see which has the features you most value.
08. Install security and anti-spam plugins

Many security features can be added with a comprehensive security plugin, such as iThemes Security or Sucuri, both of which both have free and premium versions. Security plugins come with a suite of tools to lock down vulnerabilities on your site such as those already mentioned in this article; from masking your version number, to installing two-factor authentication for logins, the feature lists are often extensive.
These types of plugins can be invaluable in making your WordPress site more secure, and most security plugins are easy to use with single-click installation for the most important features, and optional installation for the more advanced or complex features. This makes them perfect for WordPress beginners, as there's no coding needed to get a well-protected site in minutes. More advanced users will have access to features that can further secure your site, such as closing down unneeded access to protocols such as XML-RPC, and updating the WordPress salts used in encoding.
Such plugins will help to protect your site against brute force and DOS attacks, which can take your sites offline if there is too much load on the server. They can also firm up the login process with additional levels of security to prevent your user accounts being used as a method of attack. Malware scanning and activity logs keep records of any suspicious behaviour or corrupted files for review, warning you of any attacks in progress and giving you an idea of where your site's vulnerabilities lie so you can resolve them.
Some security plugins also come with backup options, for that all-inclusive service. Having all of your security needs organised by one plugin means that the features are easy to organise, with less risk of conflict between similar plugins. Make sure you do your research, however, as this plugin is going to be the thing standing in the way of your site and anyone wanting to cause it harm. You will need to pick one that will do the job admirably.
Additionally, an anti-spam plugin such as Akismet will keep spammers from clogging up your site with unrelated comments. If your security plugin isn't already doing so, it can assist the security plugin by adding an extra layer of security to your community interaction by using validation tools like CAPTCHA and other anti-bot devices to make sure only real people are commenting. An anti-spam plugin helps keeps your site clean, as well as your database behind the scenes. Screening for valuable comments has the added bonus of giving your content more weight by only showing proper engagement from readers.
Each plugin comes with its own different tools, so compare the options for something that suits your needs. Consider premium versions of plugins for additional features since this is an integral part of your site and generally speaking, paid plugins will give you the most comprehensive service. Ideally you want a suite that covers at least the basics of security, such as the other tips named in this article.
This article was originally published in issue 272 of creative web design magazine Web Designer. Buy issue 272 here or subscribe to Web Designer here.
Related articles:

